Need help?
Get answers fast, or talk to us on live chat.
Start Live Chat
On March 31, 2026, one of the most widely used JavaScript libraries – Axios – became the target of a highly sophisticated supply chain attack. It really exposed a fundamental weakness in modern development infrastructure that a lot of teams still overlook.
With over 100 million weekly downloads, Axios sits deep inside frontend applications, backend services, CI/CD pipelines, and all kinds of internal automation systems. It’s so common that even a short compromise can create a surprisingly large blast radius. In this case, attackers took over a maintainer account and turned ordinary npm install commands into a silent way to push malware across thousands of environments.
What makes this attack stand out is that they didn’t exploit any traditional vulnerability in the code. Instead they used the trusted parts of the npm ecosystem itself – dependency resolution and those automatic install-time scripts – and turned normal behavior into a real attack surface.
This isnt just some package problem anymore. It’s a bigger systemic risk for how we build and run infrastructure today.
The attackers got control of the npm account that belonged to Axios’s lead maintainer. They simply changed the email address to one they controlled on ProtonMail. That move locked out the real owner and gave the attacker full rights to publish new versions.
From there they released two malicious versions:
Both versions quietly pulled in a phantom dependency called
This package was never actually used or called by Axios code at all. Its only job was to serve as a delivery vehicle for the malicious payload through npm’s lifecycle hooks.
To make it less suspicious the attackers first published a clean version plain-crypto-js@4.2.0 about 18 hours earlier. That trick helped the bad update blend in with regular package activity and slip past the basic checks that automated scanners usually run.
The malicious versions only stayed live for roughly 2 to 3 hours. But in that short window any system running npm install – on a developer laptop, inside a CI/CD pipeline, or during an automated deployment – could have quietly installed and triggered the payload.
The whole attack depended on npm doing what it normally does: running lifecycle scripts automatically when you install a package.
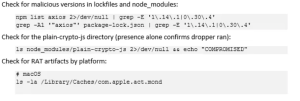
As soon as the malicious dependency landed, its package.json fired a postinstall hook. That hook ran a dropper script called setup.js without any user interaction needed.
The dropper went through these steps:
The second-stage payload turned out to be a full Remote Access Trojan. It could do things like:
Credential harvesting including SSH private keys, cloud credentials from AWS GCP and Azure, plus npm and GitHub tokens.
System reconnaissance such as hostname, user details, OS version, installed applications and running processes.
File system access for directory enumeration, finding sensitive files and quietly exfiltrating them.
Remote execution so it could run arbitrary commands or drop additional payloads.
And persistence that let it keep running in the background even after the original install finished.
To stay hidden the malware cleaned up after itself pretty effectively. It deleted its own installation scripts once the job was done, replaced the package.json with a clean version, mimicked normal package metadata, and made sure to suppress any errors so the npm install would finish without showing problems.
Because of these tricks npm audit didnt flag anything, npm list looked perfectly clean, and users saw no visible errors. The only real signs were at the filesystem level or in network traffic – stuff most people don’t check during a regular install.
This attack makes one thing very clear: every time you run a dependency installation you’re allowing code to execute inside your infrastructure without really thinking twice about it.
Once it ran the attack could pull sensitive assets such as AWS IAM keys, GCP service accounts, Azure tokens, .env files, API keys, OAuth tokens, SSH private keys, database connection strings and CI/CD secrets that get injected at runtime. It basically turned a simple dependency install into a full infrastructure breach and it often did so without setting off any obvious alerts.
The dangerous part is that this attack did not rely on a bug. It used behavior that was intentionally built into the system – and that’s exactly why its so risky.
npm lifecycle hooks allow automatic code execution during installation.
There is no sandbox, no permission system, and no user confirmation — it runs with full privileges.
Even unused dependencies can execute code, making this a
critical attack vector.
The malware hid its tracks by modifying scripts, replacing package.json, and spoofing metadata.
As a result, tools like npm audit and npm list showed no issues,
and manual checks appeared normal.
Detection required deeper methods like filesystem inspection, network monitoring, and behavioral analysis.
Even with OIDC-based publishing, legacy authentication methods like long-lived tokens remain active.
This creates a dangerous gap: a secure path exists, but the
insecure fallback is still enabled.
At Netrouting we treat infrastructure security as a multi-layered responsibility that goes well beyond traditional perimeter defenses.
Supply chain attacks like this one show that threats can come from inside trusted internal processes not only from outside hackers.
We help organizations lower this risk by isolating build environments from production, adding strict network segmentation and egress filtering, supporting zero-trust architectures, enabling runtime monitoring for unusual behavior and reducing where credentials are exposed across layers. That way even if a dependency gets compromised its impact on the rest of the environment stays limited.
If any system ran
during that exposure window you should treat it as fully compromised. It’s better not to try cleaning it up in place – just rebuild everything from a known-good baseline.

Static scanning alone is no longer sufficient against modern supply chain threats.
Dependency installation is really an execution event now.
CI/CD pipelines have become high-value attack targets.
Trust-based ecosystems bring systemic risks.
Detection needs to shift from just looking at code to watching runtime behavior.
Isolation and control often work better than trying to prevent everything upfront.
The Axios supply chain attack shows a clear shift in how modern infrastructure gets compromised.
It didn’t need fancy vulnerabilities or exploits. Instead it took advantage of trust, automation and the default behaviors baked into the ecosystem.
For infrastructure teams the main takeaway is simple: security has to move beyond just protecting the code. We need to focus on controlling the environments where that code actually runs.
In a world where every npm install can potentially execute arbitrary code, real resilience depends on better visibility, strong isolation and tight control over the whole software supply chain.
Subscribe to our newsletter