Running a successful online business in today's highly competitive digital landscape requires far more than simply sourcing high-quality products, designing a visually appealing user interface, and refining your checkout flow for maximum conversions. It absolutely demands an ironclad, enterprise-grade defense system capable of stopping sophisticated, relentless cyber attacks dead in their tracks. Cybercriminals actively and aggressively target digital storefronts because they operate as highly lucrative, centralized treasure troves of highly valuable customer data, credit card details, and personal identities.
Implementing strict, comprehensive ecommerce Security Measures is no longer just an optional IT upgrade, a secondary concern, or a luxury reserved solely for massive, multinational corporations. It has evolved into the absolute fundamental baseline for keeping your digital doors open, safeguarding your hard-earned brand reputation, and protecting your underlying infrastructure from catastrophic malware infections. If you want to survive, scale, and thrive in the modern web environment, building strong ecommerce security has to be natively baked into your daily operations, your server architecture, and your corporate culture. The stakes have never been higher, as a single vulnerability can unravel years of hard work.

Why Most eCommerce Websites Get Hacked
Let's clear up a massive, pervasive misconception right now. The vast majority of digital storefronts are not getting breached by a dedicated team of elite hackers sitting in a dark room, specifically hand-picking your brand for a targeted assault. In 2021, 50% of all cyber-attacks targeted small and medium-sized businesses (SMBs), making e-commerce sites particularly vulnerable due to their rich data sources. The reality of modern cyber warfare is usually much less personal and far more automated. Attackers deploy massive, highly efficient botnets that relentlessly scan the entire internet, probing thousands of servers per minute, looking for incredibly easy targets.
Blog contents
These automated scripts are endlessly hunting for known vulnerabilities, such as outdated software frameworks, inherently lazy administrative passwords, completely insecure, unpatched hosting environments, and exposed databases. Once these relentless bots find a tiny crack in your digital armor, they move with terrifying speed. They will automatically inject destructive malicious code, set up deeply hidden backdoors for future exploitation, or drop crippling malicious software onto your server before you even realize what hit you. Without aggressive, multi-layered security measures fully active in place, your site is practically leaving its front door wide open. Failing to prioritize e commerce security actively invites an army of cyber threats to completely gain unauthorized access to your most critical backend systems and sensitive databases.
The True Cost of Data Breaches and Lost Customer Trust
Getting hit with a severe malware infection or a targeted ransomware attack is an absolute, unmitigated financial nightmare for any organization. Sure, the immediate, tangible theft of digital inventory or hijacked, redirected transactions hurts badly. But the long-term, lingering damage is what truly paralyzes and ultimately destroys growing e commerce businesses.
When Google or other major search engines detect embedded malicious code on your primary domain, they will actively blacklist you almost instantly to protect their search users. Your hard-earned SEO rankings, which likely took years and thousands of dollars to build, will tank overnight, completely destroying your organic traffic pipeline. On top of that devastating loss of visibility, public data breaches cause irreversible, permanent damage to your brand's reputation. If your loyal buyers eventually find out you failed to adequately safeguard customer data, you lose their customer trust forever. Nobody is ever going to willingly risk facing identity theft or stolen finances just to buy a product from your store.
Rebuilding that shattered trust, dealing with the massive legal headache of refunding fraudulent transactions, hiring expensive forensic server analysts, and paying off massive regulatory fines will easily bankrupt a small to mid-sized online store. A single, preventable breach can completely disrupt business operations so severely that it permanently ruins growing ecommerce businesses and the financial lives of the consumers trusting them.
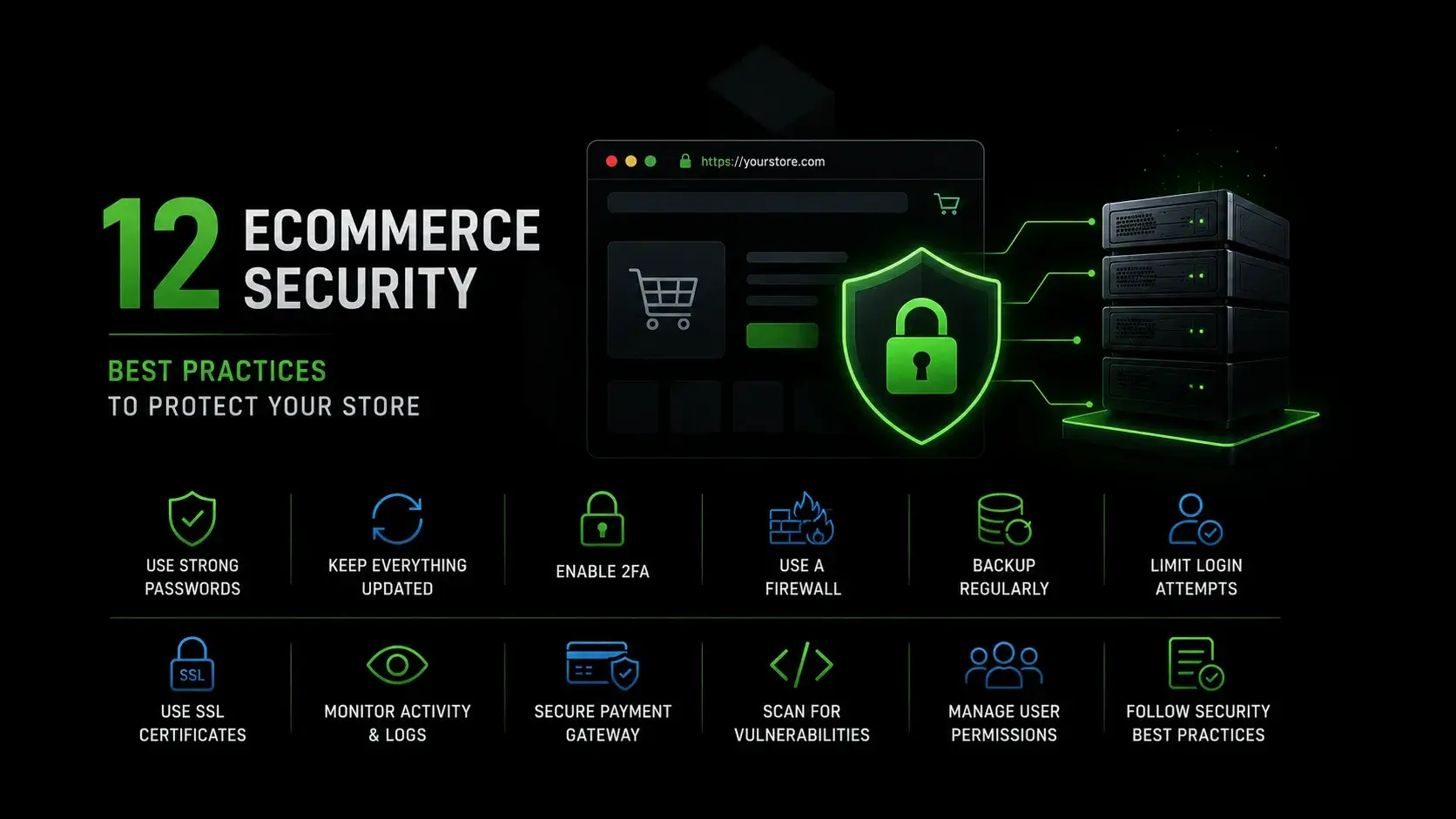
12 eCommerce Security Best Practices to Protect Your Store
Protecting your primary revenue stream requires a highly proactive, deeply layered approach to network architecture. You simply cannot rely on a single, cheap, set-it-and-forget-it security plugin to do all the heavy lifting against sophisticated syndicates. Using multi-layer security, which includes firewalls, antivirus software, and regular updates, helps create a robust defense against various cyber threats targeting e-commerce platforms. By implementing these twelve foundational, non-negotiable steps, you can build a highly resilient, impenetrable wall between your sensitive customer data and the global networks of attackers constantly trying to steal it.
1. Use SSL Certificate and Enforce HTTPS
This particular security step is completely, unquestionably non-negotiable in the modern era of web routing. A secure sockets layer (SSL) certificate utilizes complex cryptographic protocols to perfectly encrypt the data moving back and forth between your customer's web browser and your primary web server. It is the exact technology that gives your store that reassuring little padlock icon in the URL bar and forces the mandatory "HTTPS" secure connection status.
You absolutely must deploy premium ssl certificates to create an unbreakable encrypted connection across every single page of your site, not just the checkout portal. If you stubbornly skip this step or let your certificate expire, critical, highly targeted information like login credentials, home addresses, and payment details are transmitted across the open internet in readable plain text. That massive oversight makes it laughably easy for attackers to execute packet-sniffing operations and steal sensitive information right out of thin air. To completely lock this down, HTTP Strict Transport Security (HSTS) forces all connections over secure channels, guaranteeing no user can accidentally load your site over an unencrypted connection.
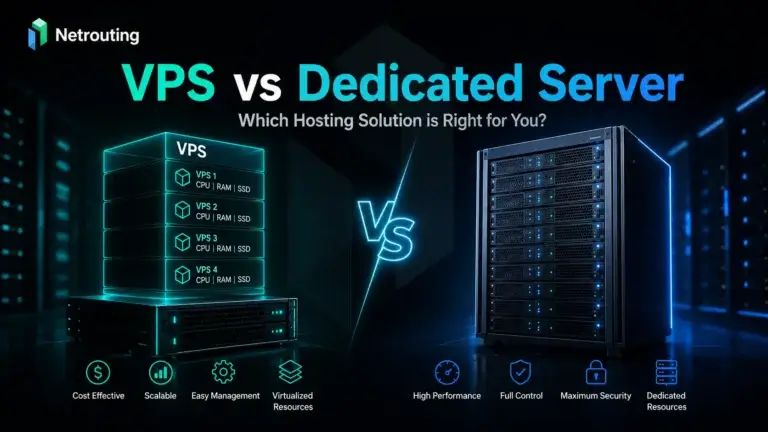
2. Choose Secure Hosting Infrastructure
Your entire online shopping platform is fundamentally only as strong, fast, and secure as the underlying physical server hardware hosting its files. Cheap, bargain-bin shared hosting plans are notoriously dangerous breeding grounds for causing massive, systemic security risks. If another completely unrelated website residing on your shared server environment gets compromised due to their own negligence, the resulting malware infection can easily bleed over into your directories and corrupt your files.
To truly isolate and protect sensitive data, you need to migrate to a premium, deeply isolated hosting environment. Moving to a dedicated bare-metal server means you absolutely are not sharing CPU, RAM, or storage resources with anyone else. This hardware-level isolation keeps your data security incredibly tight, prevents cross-contamination, and ensures you always have the raw computing power necessary to handle massive seasonal traffic spikes without ever crashing or dropping secure connections. Additionally, implementing a failover system can improve the availability of your e-commerce site by switching to redundant installations when the primary environment is unavailable, ensuring continuous service for customers.

3. Keep Software, Plugins, and Themes Updated
Running old, outdated code in a production environment is basically writing an open invitation to be hacked. Whenever platform developers, third-party plugin creators, or your theme designers push a new update, they are almost always patching newly discovered, publicly documented security gaps. Hackers actively read these patch notes to reverse-engineer exploits for older versions.
If you constantly drag your feet, ignore those critical update notifications, and leave legacy code running, automated bots will eventually scan your e commerce site, identify the version number, and exploit those exact flaws to forcefully gain access to your backend architecture. Staying incredibly strict and religious about your weekly update schedule is one of the easiest, cheapest, and absolute most effective ways to completely neutralize thousands of known cyber attacks before they ever execute.
4. Enable Multi-Factor Authentication (MFA)
Massive caches of stolen passwords are leaked onto the dark web every single day. Because everyday people constantly reuse the exact same weak passwords across dozens of different websites, these massive data dumps make valid logins publicly available to hackers for pennies. That is exactly why you absolutely need to enforce multi factor authentication for all of your administrative user accounts, and ideally offer it to your retail buyers as well.
If your system strictly requires a secondary text message code, a biometric scan, or a time-sensitive authenticator app to log in, a stolen password becomes completely, utterly useless to the attacker. Using multi-factor authentication is considered a best practice for enhancing security in e-commerce, as it helps protect customer accounts and sensitive data from cyber threats. Implementing robust multi factor authentication mfa effectively stops hackers right at the initial login screen, creating a hard physical barrier that prevents unauthorized entry even if they have successfully acquired the correct username and password combination.
5. Use Strong Password Policies
You have to immediately stop letting your development team, your marketing staff, and your customers use variations of "password123" or their company name. You need to forcefully enforce strong passwords across the entire board at the software level. Make the registration and account creation process require a long, complex mix of upper and lower case letters, numbers, and special symbols.
This strict entropy requirement is your absolute best, most reliable defense against relentless brute force attacks, where sophisticated automated software attempts to guess millions of common dictionary password combinations per minute until it forcefully breaks the door down. Proper, rigorous access management means ensuring that one employee's incredibly weak, easily guessable password isn't the single weak link that brings down the network, severely compromising both the business and the consumers who rely on it.

6. Perform Regular Automated Backups
If a highly sophisticated ransomware attack somehow bypasses your firewalls and successfully locks down your entire product database with military-grade encryption, a perfectly clean, highly recent data backup is your absolute only way out of bankruptcy. You cannot simply hope for the best; you need to set up a rigorous, completely automated backup schedule that requires zero human intervention.
Adhere strictly to the industry-standard 3-2-1 backup rule: you must keep three total, distinct copies of your data, stored safely on two entirely different types of physical or digital media, with at least one complete copy kept securely off-site in an isolated, air-gapped server environment. Having these reliable backups means you can confidently wipe an infected ecommerce store clean and restore operations quickly without ever being forced to pay off anonymous cybercriminals to regain access to your own livelihood. Regularly creating backups of your e-commerce site minimizes downtime and data loss in the event of a security breach or system failure.
7. Install a Web Application Firewall (WAF)
Think of intelligent web application firewalls as the heavily armed, highly perceptive bouncers for your entire digital operation. They sit directly between your digital storefront and the wild, unfiltered internet, actively inspecting every single packet of incoming traffic. They are designed to block shady requests, aggressively filter out spam bots, and neutralize known threat signatures before they ever reach your core application files.
A solidly configured WAF is specifically programmed to catch and drop malicious attempts to run cross site scripting or inject code into your database, giving you a massive, proactive advantage in overall ecommerce security. Without a WAF filtering the noise, your web server has to process every single malicious request, wasting bandwidth and leaving you highly vulnerable to application-layer manipulation.
8. Protect Against DDoS Attacks
A calculated distributed denial of service (DDoS) attack is designed to brutally, mercilessly crash your site by flooding its bandwidth and CPU with an overwhelming, impossible amount of fake, automated traffic. When your server cannot process the sheer volume of requests, it simply shuts down. You need dedicated, network-level mitigation tools that can automatically absorb, analyze, and reroute this junk traffic away from your primary IP address so your real, paying buyers can still get to the checkout page without experiencing timeouts.
Attackers frequently use disruptive DDoS attacks as a noisy, chaotic smokescreen to distract your IT team and hide other common ecommerce security threats happening simultaneously, so having deeply enhanced security and specialized routing in this specific area is incredibly vital to your uptime.
9. Monitor Suspicious Activity in Real-Time
You fundamentally cannot fight an ongoing attack if you have absolutely no idea it is currently happening. You must set up advanced, highly tuned monitoring tools that flag weird, anomalous server behavior instantly and send alerts to your administration team. If an unknown entity tries logging into an admin account from a foreign country twenty times in a two-minute window, or if thousands of files are suddenly modified simultaneously, you need a blaring alarm.
Constantly auditing and checking your real-time access logs gives you the precise visibility and situational awareness you need to identify and physically sever a threat's connection before they manage to permanently exfiltrate massive volumes of information to an external server. Furthermore, an incident response plan should be documented and tested to respond effectively to breaches the absolute second these monitoring tools trigger a critical alert.
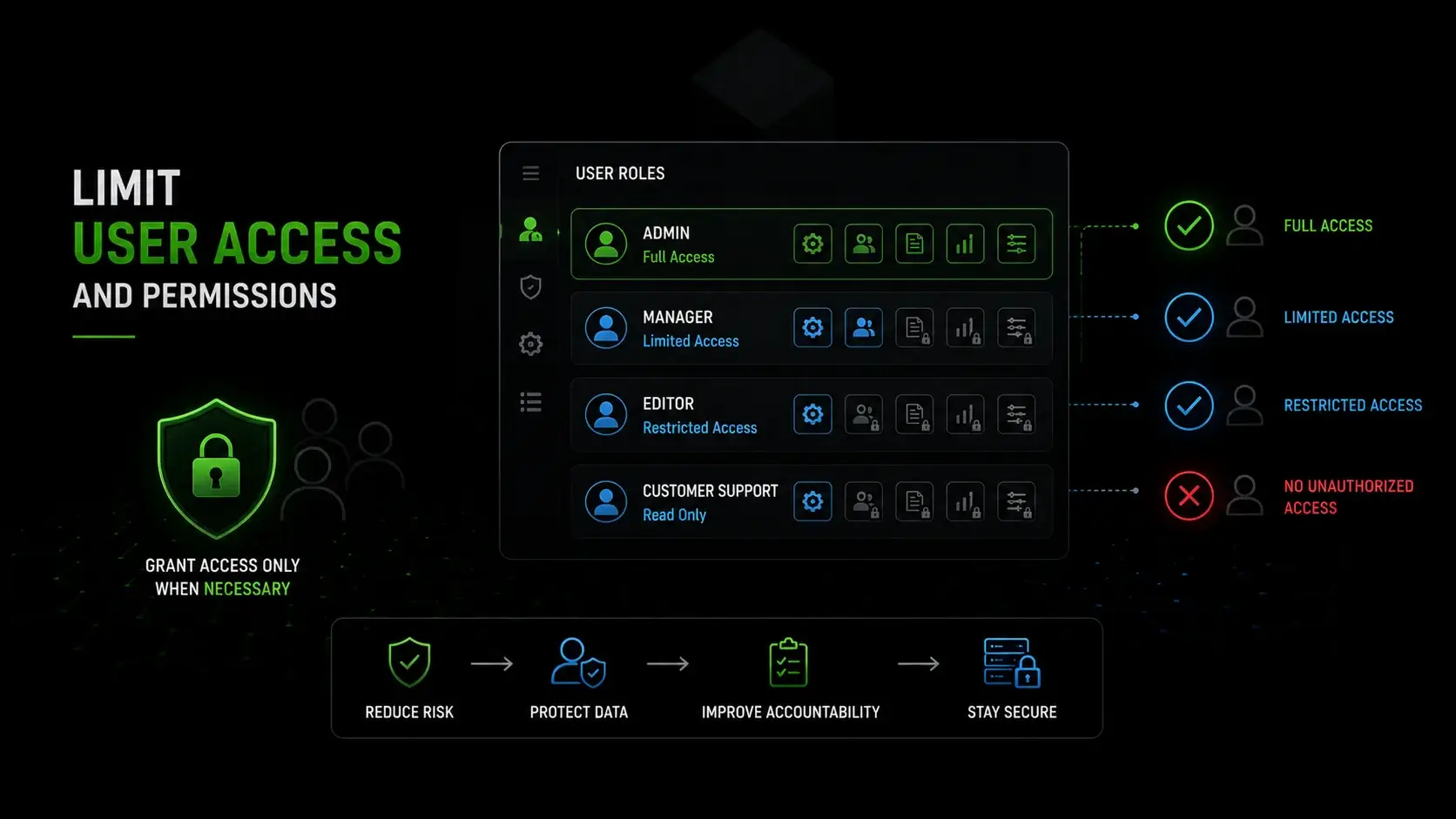
10. Limit User Access and Permissions
Not everyone on your corporate payroll needs to hold the master keys to the digital kingdom. You must stick rigidly to the established cybersecurity principle of strict, zero-trust access control. A frontline customer support representative dealing with shipping inquiries only needs to see basic order histories; they absolutely do not need root access to core server settings, source code repositories, or raw, unencrypted financial data. Role-Based Access Control (RBAC) limits employee access to specific data and systems necessary for their jobs. Limiting these permissions through role-based access severely minimizes the potential blast radius and overall damage if a lower-level employee's account gets compromised.
Limiting these permissions through role-based access severely minimizes the potential blast radius and overall damage if a lower-level employee's account gets compromised via a clever phishing email. By compartmentalizing your network, you ensure that a single compromised endpoint does not result in a total system collapse.
11. Secure Payment Processing and Prevent Fraud
You should never, ever attempt to store full, unencrypted cardholder data directly on your own physical servers or internal databases. It is a massive, unnecessary liability that makes you the ultimate target for organized cybercrime syndicates. Instead, always utilize highly reputable, industry-leading secure payment gateways that use advanced tokenization methods.
Let the massive, heavily regulated financial institutions handle the incredibly heavy lifting, complex encryption, and strict legal compliance of payment processing. Additionally, relying on their highly tuned, built-in fraud detection algorithms and address verification systems helps aggressively cut down on the fraudulent purchases and subsequent chargebacks that eat directly into your hard-earned profit margins. You must also remain highly vigilant against emerging injection threats. E-skimming, also known as Magecart attacks, involves injecting malicious code into checkout pages to capture credit card details in real time, posing a significant threat to e-commerce security.
12. Run Regular Security Scans and Penetration Testing
Do not just sit around comfortably waiting for a malicious hacker to find your network's weak spots first. You must be proactive by using advanced, automated vulnerability scanners to routinely check your entire infrastructure for newly discovered software exploits and misconfigurations.
Doing this weekly as a core, unyielding part of your continuous monitoring strategy lets your engineering team quickly patch things up before they become a massive, public problem. Staying aggressively proactive, constantly searching for your own flaws, is the absolute master key to successfully protecting customer data in a landscape where the threats evolve on a daily basis.

Advanced Security Measures and Server Protections
While the basic digital hygiene steps outlined above are fantastic for keeping automated bots and script kiddies away from your perimeter, rapidly growing enterprises processing high volumes of transactions need highly advanced security measures to actively fight off deeply targeted, incredibly sophisticated attacks. This requires stepping far beyond simple WordPress plugins and locking things down tightly right at the bare-metal infrastructure level.
Deploy a Web Application Firewall (WAF)
At the heavy enterprise level, your WAF needs to be far more than a basic filter; it needs to be deeply integrated into your entire routing architecture. Instead of just relying on a basic, off-the-shelf cloud proxy, an advanced, enterprise-grade WAF lets your security engineering team write highly complex, custom rulesets specifically tailored for your site's unique codebase and framework logic.
sql injection attacks allow unauthorized users to access databases filled with customer information by inserting malicious code into input fields, which can lead to data breaches. An advanced WAF actively intercepts these deep Layer 7 attacks, successfully neutralizing highly complex sql injection attempts, malicious API abuse, and dangerous cross site scripting xss payloads right at the extreme edge of your network. It completely destroys the threat before the bad packets can even reach or manipulate your backend databases.
Utilize Next-Gen Antivirus and Vulnerability Scanning
Standard, old-school antivirus software just checks incoming files against a static list of known virus signatures. That archaic method is simply not enough anymore to stop modern syndicates. You need next-generation endpoint detection and response (EDR) software that utilizes advanced machine learning, heuristics, and deep behavioral analysis to instantly spot brand new, completely undocumented zero-day threats.
These advanced systems constantly scan your server's active memory allocations and file system integrity to catch, isolate, and terminate malicious software before it can execute its payload, ensuring your server remains pristine even when attacked by highly evasive, polymorphic malware.

Perform Regular Penetration Testing
Deep penetration testing involves actively allocating budget to hire elite, highly trained ethical hackers to intentionally attack your live production infrastructure. They do not just run automated tools; they manually, methodically probe your network routing, server configurations, and underlying application logic to uncover deep-seated, complex vulnerabilities that automated scanners completely miss.
This human-led, highly aggressive approach simulates exactly how a real, highly motivated attacker would attempt to bypass your firewalls to steal your financial information, giving your engineering team a highly detailed, actionable roadmap to permanently fix your cyber security posture.
Monitor for Suspicious Activity and Real-Time Threats
Take your internal network monitoring up a massive notch by fully integrating all of your server, application, and firewall logs with a dedicated Security Information and Event Management (SIEM) system. A SIEM pulls incredibly massive amounts of raw, disparate data from every corner of your infrastructure into one unified, highly analytical dashboard.
This comprehensive visibility lets a dedicated internal security team or an outsourced Security Operations Center instantly spot and shut down active, ongoing threats or quiet, low-and-slow brute force attacks in absolute real-time, allowing them to manually close the connection and ban the IP block before any actual data is ever lost.

eCommerce Security Compliance and Data Protection
Keeping your digital store locked down tightly isn't just about avoiding the massive headaches of server restoration; it is a strict, completely unavoidable legal obligation. If you fail to rigorously adhere to global, standardized data security protocols, you are looking at devastating, brand-ending class-action lawsuits, massive government regulatory fines, and potentially losing your merchant ability to process credit cards entirely.
Understanding PCI-DSS Requirements
The Payment Card Industry Data Security Standard (PCI-DSS) is an incredibly rigorous, non-negotiable set of operational rules mandated heavily by the world's major credit card brands like Visa, Mastercard, and Amex. It forcefully dictates that you must maintain completely secure systems, perfectly encrypt all data during transit over public networks, and meticulously test your security setup on a regular schedule.
If your business directly handles payment information, stores routing numbers, and processes online transactions, achieving and flawlessly maintaining strict PCI compliance is the absolute only way to prevent massive financial fraud liabilities and legally stay in business. Achieving and maintaining PCI DSS compliance involves establishing a secure network, protecting cardholder data, maintaining a vulnerability management program, implementing strong access controls, and regularly monitoring and testing networks. Failing a PCI audit can result in immediate termination of your payment processing agreements.
GDPR and CCPA Compliance for Customer Data
Compliance with regulations like the General Data Protection Regulation (GDPR) and the California Consumer Privacy Act (CCPA) is essential for ecommerce businesses to protect customer data and avoid legal penalties. Sweeping global privacy laws strictly dictate, down to the exact letter, how you must legally collect, process, and securely store personal tracking info.
You have to be completely transparent about cookie usage, store the captured data safely using modern encryption standards, and importantly, be able to completely purge and delete a user's record from your servers if a customer officially requests the right to be forgotten. Additionally, data minimization involves collecting and storing only the minimal required customer data for transactions. By deliberately not storing unnecessary records, you limit your liability and prove to the market that you actually care deeply about efforts to protect customer information.
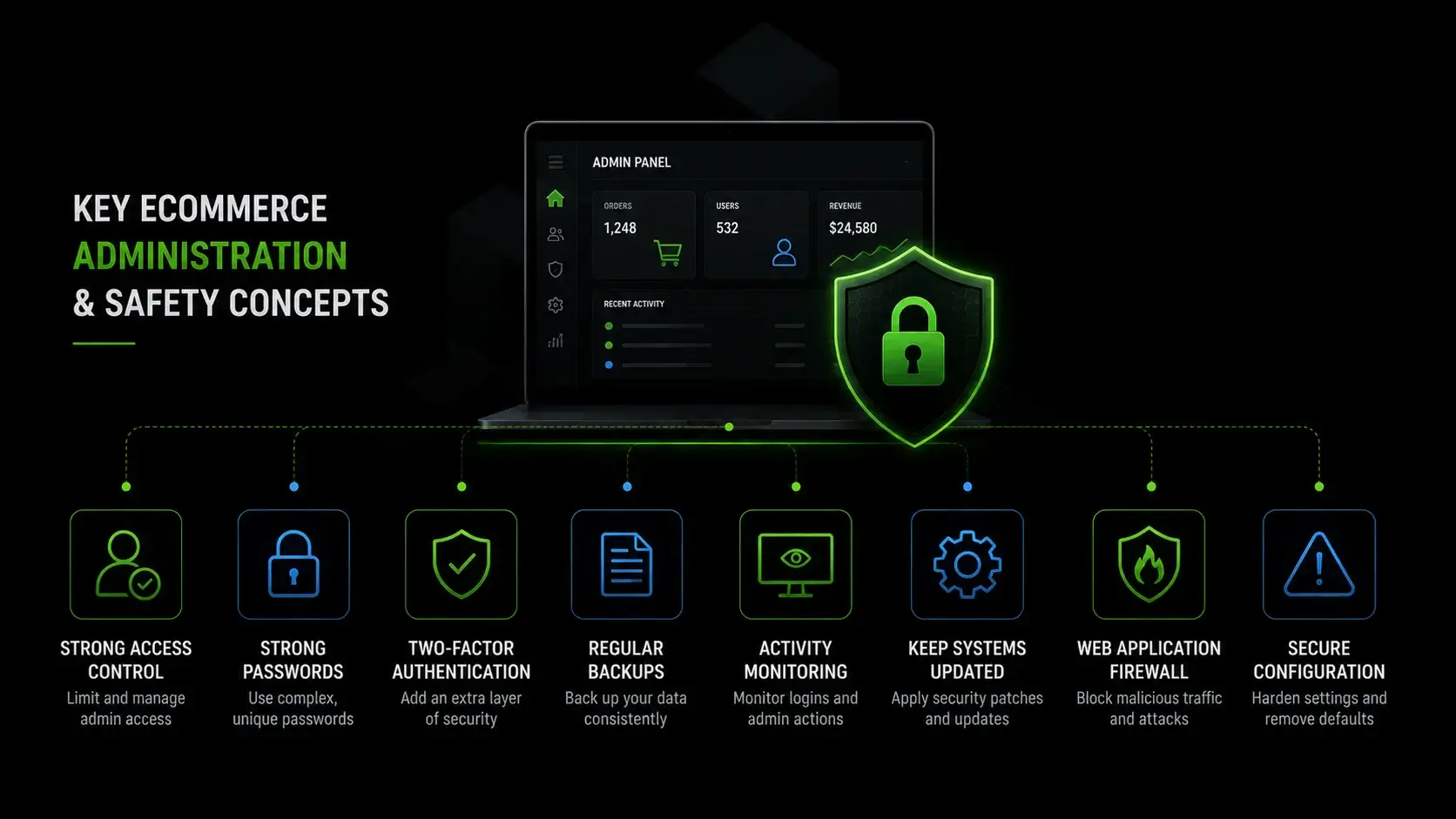
Key eCommerce Administration and Safety Concepts Explained
You can go out and buy the absolute strongest bare-metal servers, deploy the most expensive enterprise firewalls on the planet, and hire the best developers, but if the actual human beings running your daily operations get lazy or careless, you are still going to get hacked. Securing the habits of your administrative team is the final, most critical, and often most difficult layer of your holistic defense against modern ecommerce security threats.
Educating Employees and Customers on Security Protocols
Human error and psychological manipulation remain the leading causes of massive, catastrophic network breaches worldwide. Implementing a solid, recurring employee training program helps your internal staff quickly and accurately recognize highly sophisticated, targeted phishing emails designed specifically to steal their high-level logins.
Furthermore, you also need to gently but firmly educate your retail buyers about adopting safe password habits, the growing importance of verifying digital signatures on official emails, and exactly how your company will, and more importantly, will not, communicate with them. This proactive communication severely limits the chances of your customers falling for elaborate spoofing scams conducted by third parties trying to leverage your brand name.
Limiting Administrative Access to Sensitive Data
You must rigidly lock down your entire administrative backend using a strict, unyielding zero-trust approach to network architecture. Administrative access to your core infrastructure should always require passing through highly encrypted VPN tunnels, strict IP address whitelisting, and mandatory, hardware-based MFA.
If a hacker somehow manages to brilliantly break through your heavy outer perimeter defenses, strict internal compartmentalization ensures they are immediately trapped in a low-level sandbox. They cannot easily pivot laterally across the network to escalate their privileges and steal your highly sensitive data.
Utilizing Secure SFTP and SSH Connections
You must ensure your web developers never, under any circumstances, use vastly outdated, inherently unencrypted File Transfer Protocol (FTP) clients to move core application files to your live server. Old FTP sends critical administrative passwords across the internet in highly readable plain text.
Always force your entire engineering team to exclusively use Secure FTP (SFTP) or Secure Shell (SSH) connections when communicating with the backend. These modern, highly secure protocols utilize incredibly heavy, unbreakable cryptographic encryption, meaning your developers can push code updates and manage the web server safely from anywhere in the world without the terrifying fear of anyone successfully snooping on the network traffic.
Frequently Asked Questions About eCommerce Security
- What is the most common security threat to an ecommerce website?
The absolute most frequent threat isn't a highly targeted, cinematic heist; it is automated botnets. These malicious scripts constantly scour the entire internet looking for ecommerce sites running outdated platform software, vulnerable third-party plugins, or incredibly weak administrator passwords. Once they find a gap, they instantly inject malicious code or deploy ransomware. Phishing attacks specifically targeting your staff's login credentials to steal credit card details are also incredibly common and highly effective.
- Is standard shared hosting safe enough for my online business?
For a growing online business that handles sensitive customer data and active payment information, basic shared hosting is simply too risky. If another completely unrelated website on your shared server gets infected with malicious software, that infection can easily bleed over into your directories. To fully protect sensitive data and maintain strong ecommerce security, migrating to an isolated, dedicated web server is considered the industry standard to completely eliminate cross-site contamination.
- What actually happens if I ignore PCI-DSS compliance?
If you process online transactions and choose to ignore strict PCI compliance rules, the financial consequences are severe. You will face massive, compounding monthly fines from the major credit card networks. More importantly, if a catastrophic data breach occurs and forensic investigators find you were legally non-compliant, you can be permanently banned from processing credit cards ever again. For most e commerce businesses, losing the ability to take digital payments means shutting down overnight.
- How often should I back up my ecommerce database?
If your store is actively generating daily sales, you must be running fully automated backups at an absolute minimum of once every 24 hours. However, for high-traffic online stores, real-time or hourly database backups are the ultimate best practice. You must always follow the 3-2-1 backup rule: keep three total copies of your data, on two different media types, with one stored completely off-site on a secure server. This guarantees you can recover your customer information without ever paying a ransom.
- Does an SSL certificate completely protect my store from hackers?
No, it does not. An SSL certificate is absolutely mandatory, but it only performs one specific, limited job: it creates an encrypted connection between your customer's web browser and your server so data cannot be actively intercepted in transit. It does absolutely nothing to protect your core files from an sql injection, aggressive brute force attacks, or cross site scripting xss. To achieve true data security, you must combine your SSL with an advanced web application firewall, strict access, and continuous monitoring.